Moving data from bytes to terabytes
Better Performance and Throughput Efficiency
5× faster, 40% better system throughput through multi-threading innovation
AI Accelerator: Offload Core Processing
30% better AI stack software utilization and efficiency
Proven Automotive Solution
Deployed in 70% ADAS for L2+ front facing cameras globally
Cost-Effective and Scalable
From real-time latency sensitive cores to high-performance multi-core/cluster chiplets
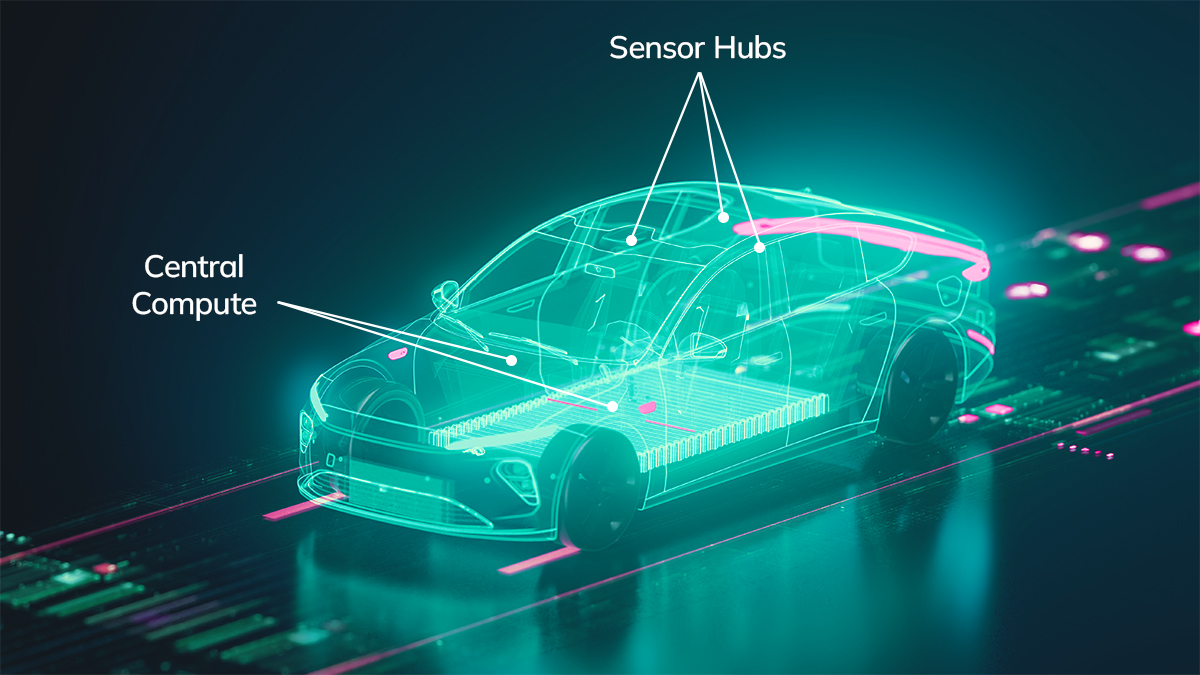
Advanced Driver Assistance Systems (ADAS)
MIPS delivers highly efficient data movement to support multiple high-speed and high-resolution sensors that need to be processed with very low latencies.
- 40% higher system throughput and efficiency for data movement intensive workloads (like ADAS L2/L3 Systems)
- Lower SOC or Chip power and SOC or Chip size area compared to other solutions – due to architecture built for automotive end applications
- Scalable from low end to high end systems with configurable multi-core and multi-cluster designs
Software-Defined Vehicle (SDV)
The new paradigm of software-first, Over the Air (OTA) updates requires a change in the design and architecture of the underlying electronic components that power the Software Defined Vehicles (SDVs) of the future.
- Both hardware and software co-design to providing a digital twin to test and validate new features post deployment
- Compute solutions need to provide not only the performance, efficiency and scalability needed for these advanced systems but also need to provide the headroom and flexibility to enable these SDVs
- MIPS Compute IP Subsystems provides the best compute density and solutions for these SDVs of the future.
Introducing the MIPS P8700
Industry’s First AI-Enabled RISC-V Automotive CPU for ADAs and Autonomous Vehicles
The MIPS Multi-threading and other architectural hooks tailored for automotive applications make it a compelling core for data- intensive processing.- Enables high-performance compute systems which consume less power
- Better utilizes AI acceleration
- Built on proven MIPS micro-architecture deployed in 28+ car models today across global OEMs
MIPS RV64 P8700/P8700-F Multiprocessing System Programmer’s Guide
Revision 1.83
April 9, 2025
The updated P8700 programmer’s guide adds version numbering entry to each individual instruction.
Updated Table B.1 in Appendix B to include family name and version number for each instruction.
MIPS Releases P8700, Industry’s First High-Performance AI‑Enabled RISC‑V Automotive CPU for ADAS and Autonomous Vehicles
MIPS, a leading developer of efficient and configurable IP compute cores, announced today the general availability(GA) launch of the MIPS P8700 Series RISC-V Processor. Designed to meet the low-latency, highly intensive data movement demands of the most advanced automotive applications such as ADAS and Autonomous Vehicles (AVs), the P8700 delivers industry-leading accelerated compute, power efficiency and scalability.
P8700 Multiprocessing System Datasheet
The MIPS® P8700 Multiprocessing System (MPS) is a member of the MIPS 8th Generation Architecture family. In addition to full compatibility to RISC-V technology by supporting the RV64GC Base ISA and Standard Extensions, the MIPS 8th generation architecture also brings MIPS-extended features already proven in MIPS ISA-based cores to enhance the performance and functions on running applications.

“MIPS has been a key collaborator in our success with the EyeQ™ systems-on-chip for ADAS and autonomous vehicles,” said Elchanan Rushinek, Executive Vice President of Engineering for Mobileye. “The launch of the MIPS P8700 RISC-V core will help drive our continued development for global automakers, enabling greater performance and excellent efficiency in cost and power usage.”
“We are excited to support MIPS in the development of their next-generation RISC-V processor cores and support our mutual customers with this pre-verified solution,” said Michal Siwinski, CMO of Arteris. “This partnership underscores our commitment to support the broader ecosystem by delivering RISC-V ready NoC interconnects that not only enhance performance and reduce SoC power, but also improve scalability for future electronic innovations.”
“We are excited to work on the safety qualification of the new MIPS P8700 core that will be used in Mobileye EyeQ7 and continue the strong relationship between the companies to qualify MIPS products.”, said Dr. Francesco Rossi, Emdedded Safety Solution Director, RESILTECH. “The results are good and will be of great value to System on Chip vendors.”
Design and Innovate with MIPS Today
Start designing with Accelerated Automotive Compute today for high-performance, low power and highly efficient cores.
